Understand PPSM network boundaries on NIPR, how they work, and why they matter for secure military network access.
PPSM network boundaries on NIPR are controlled checkpoints that regulate which ports, protocols, and services can pass between systems, ensuring only authorized communication occurs on the network.
I remember staring at the phrase “PPSM network boundaries on NIPR” and thinking… This sounds way more complicated than it should be.
It felt like one of those terms designed to keep outsiders out. Like you needed clearance just to understand the sentence.
But the deeper I went, the more I realized something unexpectedly simple hiding underneath all that complexity:
This isn’t just about networks. It’s about control.
It’s about deciding what gets through, and what doesn’t.
And once that clicked, everything else started to make sense.
What Are PPSM Network Boundaries on NIPR?
At its core, PPSM (Ports, Protocols, and Services Management) is about controlling how systems communicate.
Now layer that onto NIPR, the Non-classified Internet Protocol Router Network, and you get an environment that must stay operational while still being tightly secured.
So where do network boundaries come in?
They act as controlled gateways between systems.
They inspect traffic.
They enforce rules.
They decide what is allowed.
In simple terms:
PPSM network boundaries on NIPR are the enforcement points where communication is filtered based on strict approval rules.
Why PPSM Network Boundaries Exist
Here’s something that doesn’t get talked about enough:
Most security failures don’t happen because of brilliant hackers.
They happen because something was left open.
A port that shouldn’t be.
A service no one reviewed.
PPSM exists to prevent exactly that.
The Core Purpose
- Reduce unnecessary exposure
- Standardize communication across systems
- Minimize attack surfaces
- Enforce strict compliance
Quotable insight:
“Reducing open ports directly lowers the risk of unauthorized access in controlled networks.”
But here’s the tension:
Lock things down too much, and systems stop working efficiently.
Open things up too much, and risk skyrockets.
PPSM network boundaries live in that balancing act.
Breaking It Down: Ports, Protocols, and Services
Ports: The Digital Entry Points
Ports are like doors into a system.
Each one allows a specific type of communication.
- Port 80 → Web traffic
- Port 443 → Secure web traffic
If too many ports are open, it’s like leaving multiple doors unlocked in a building.
PPSM ensures only necessary doors stay open.
Protocols: The Rules of Communication
Protocols define how data is transmitted.
Examples include:
- HTTP
- HTTPS
- FTP
- SSH
Some protocols are secure. Others are outdated.
PPSM ensures only approved and secure protocols are allowed to pass through network boundaries.
Services: The Active Components
Services are what actually run on systems, like web servers or email systems.
Every active service is a potential vulnerability if not controlled.
PPSM ensures that only authorized services are exposed and accessible.
How PPSM Network Boundaries Work on NIPR
Imagine a highly secure checkpoint.
Every person passing through must be verified.
Their purpose must be clear.
That’s exactly how PPSM network boundaries function.
The Process
- A system attempts to communicate
- The traffic reaches a boundary device
- PPSM rules are applied
- The traffic is either allowed, logged, or blocked
This process happens constantly, in real time.
You don’t see it, but it’s always working.
Quotable insight:
“In controlled environments, every allowed connection is explicitly approved and monitored.”
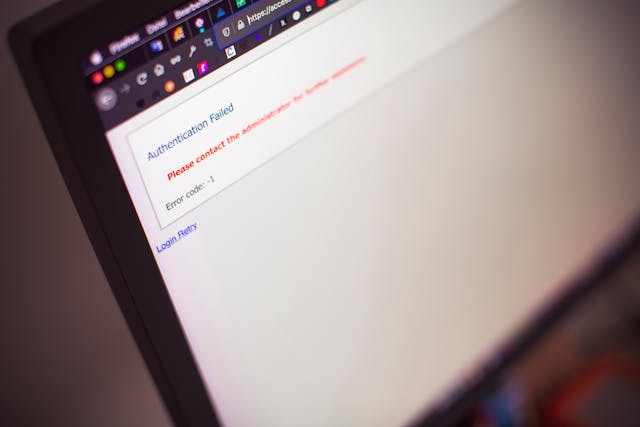
The Human Factor: Where Things Go Wrong
This is where things get interesting.
Because PPSM isn’t just about technology, it’s about people making decisions.
And people don’t always get it right.
Common Weak Points
- Misconfigured rules
- Temporary exceptions that become permanent
- Legacy systems that are hard to update
- Pressure to prioritize speed over security
That last one is especially risky.
Sometimes, someone opens access just to “fix something quickly”…
And forgets to close it later.
That’s how vulnerabilities quietly slip in.
PPSM vs Traditional Network Security
At first glance, PPSM might sound like standard firewall management.
But there’s a subtle, and important, difference.
The Shift in Thinking
Traditional security often asks:
“What should we block?”
PPSM asks:
“What is explicitly allowed, and why?”
That shift changes everything.
It forces accountability.
It demands documentation.
It reduces assumptions.
Comparison: PPSM vs Standard Firewall Approach
| Feature | PPSM Approach | Traditional Firewall |
| Philosophy | Allow by strict approval | Block by default |
| Control Level | Highly granular | Moderate |
| Documentation | Mandatory | Often optional |
| Risk Exposure | Lower when enforced | Variable |
| Flexibility | Limited | More flexible |
Real-World Scenario: Why Boundaries Matter
Let’s say a system needs database access.
Without PPSM:
- Multiple ports may be open
- Extra services could be running
- Risk increases quietly
With PPSM:
- Only one approved port is open
- Only required protocol is used
- Only verified service is active
It’s the difference between a wide-open gate…
And a single guarded entry point.
The Ongoing Challenge: Security vs Usability
This is where the real struggle happens.
Security teams want strict control.
Operational teams want speed and flexibility.
PPSM network boundaries sit right in the middle.
The Trade-Off
- Too restrictive → slows down operations
- Too permissive → increases risk
There’s no perfect setting.
Only constant adjustment.
PPSM Is Not Static , It Evolves
Networks change constantly.
New applications appear.
Old systems stick around longer than they should.
Threats evolve every day.
So PPSM isn’t something you set once and forget.
It’s continuous.
What That Looks Like
- Regular rule reviews
- Removal of unused ports
- Monitoring traffic patterns
- Updating approvals as needed
Quotable insight:
“Effective PPSM requires continuous validation, not one-time configuration.”
Why This Concept Matters Beyond NIPR
Even if you never work on NIPR, the idea still applies.
Every system relies on ports, protocols, and services.
Every system needs boundaries.
Your website.
Your apps.
Your cloud infrastructure.
The same principle holds true:
Control what gets through, or accept the risk.
FAQ
What does PPSM stand for?
PPSM stands for Ports, Protocols, and Services Management, a framework used to control network communications.
What is NIPR?
NIPR is a network used for unclassified but sensitive communication within defense environments.
Why are PPSM network boundaries important?
They restrict unauthorized communication and reduce the risk of cyber threats by controlling network access points.
Are PPSM rules permanent?
No, they are regularly reviewed and updated to match evolving network requirements and threats.
Is PPSM used outside military networks?
While PPSM is specific to certain environments, similar concepts are widely used in enterprise cybersecurity.
Key Takings
- PPSM network boundaries on NIPR define controlled communication checkpoints.
- They regulate ports, protocols, and services passing between systems.
- Their goal is to minimize risk while maintaining functionality.
- Misconfigurations are one of the biggest threats to security.
- PPSM focuses on explicitly approved communication, not assumptions.
- Continuous monitoring and updates are essential for effectiveness.
- The concept of network boundaries applies to all modern systems.
Additional Resources
- Official PPSM Guidance: A detailed overview of how ports, protocols, and services are managed in controlled network environments.